Defending the Digital World — Understanding Cybersecurity and the Top 5 Threats
Cybersecurity means protecting computers, networks, software, and data from unauthorized access, damage, theft, or disruption. It brings together people, processes, and technology to manage risk and preserve the confidentiality, integrity, and availability of information. As more aspects of life and business go digital, cybersecurity is essential for maintaining privacy, trust, and uninterrupted operations. If you want to excel in this career path, then it is recommended that you upgrade your skills and knowledge regularly with the latest Cybersecurity Training in Bangalore.

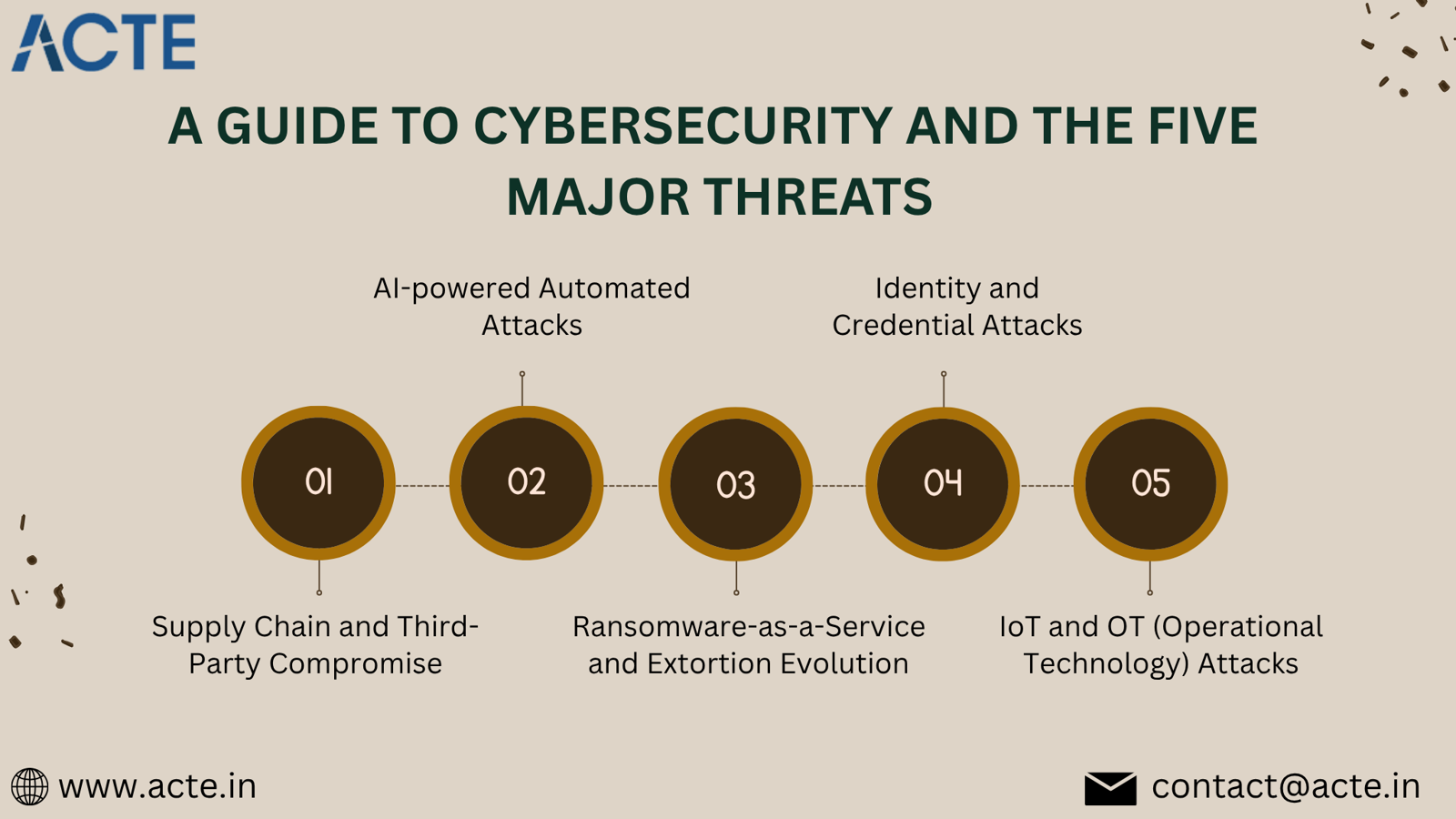
Top 5 Cybersecurity Threats (What They Are, Why They Matter, and How to Reduce Risk)
Phishing and Social Engineering
Overview: Fraudulent emails, messages, calls, or manipulated media designed to trick people into revealing credentials, installing malware, or performing harmful actions.
Why it matters: Phishing remains the most common way attackers gain initial access, leading to account takeover, ransomware, and fraud.
How to reduce risk:
- Run regular training and realistic simulations.
- Require multifactor authentication (MFA).
- Use email protection (filtering, link rewriting, sandboxing).
- Verify unusual requests through separate communication channels.
Ransomware and Extortion
Malware that encrypts data and demands payment for decryption, increasingly paired with data theft and threats to publish stolen information.
Why it matters: Ransomware can stop operations, cause data loss, and result in large financial and reputational costs.
How to reduce risk:
- Keep immutable, tested backups and offline copies.
- Patch systems promptly and secure remote access (limit VPN exposure, require MFA).
- Use endpoint detection and network segmentation.
- Maintain and rehearse incident response plans.
It’s simpler to master this tool and progress your profession with the help of Cyber Security Training which provide thorough instruction and job placement support to anyone seeking to improve their talents.
Supply-Chain and Third-Party Risks
Compromises that originate with vendors, cloud providers, or hardware suppliers and spread to their customers through updates, libraries, or integrations.
Why it matters: A single compromised supplier can impact many organizations and can be difficult to spot.
How to reduce risk:
- Maintain a detailed inventory of third parties and assess their security.
- Demand security commitments in contracts and request SBOMs.
- Apply zero-trust access for vendor integrations.
- Monitor for vendor anomalies and have contingency plans.
Cloud Misconfigurations and Access Risks
Overview: Incorrectly configured cloud services, permissive access controls, or vulnerable APIs that expose data or functionality to unauthorized parties.
Why it matters: Configuration errors are common and can expose large amounts of data or services to the public internet.
How to reduce risk:
- Use secure baseline configurations and automated scans for misconfigurations.
- Apply least-privilege access and identity governance.
- Enable comprehensive logging and monitoring for cloud resources.
- Train DevOps teams on secure cloud and Infrastructure as Code practices.
Software Vulnerabilities and Zero-Day Exploits
Flaws in software or hardware that attackers exploit to gain unauthorized access, with zero-day exploits being vulnerabilities unknown to vendors when first used.
Why it matters: Vulnerabilities enable attackers to bypass defenses, move laterally, and control systems—fueling large-scale intrusions.
How to reduce risk:
- Implement a strong patch management program and prioritize critical fixes.
- Use virtual patching and compensating controls when immediate patching isn’t possible.
- Segment networks and enforce strict access controls to limit lateral movement.
- Conduct threat hunting and use intrusion detection systems.
Conclusion
Cybersecurity is an ongoing process of managing risk—understanding threats, applying layered protections, and being ready to respond and recover. Although threats continually evolve, organizations and individuals who focus on fundamentals (strong identity controls, timely patching, reliable backups, monitoring, and user training) will significantly reduce their exposure and be better prepared when incidents occur.
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Игры
- Gardening
- Health
- Главная
- Literature
- Music
- Networking
- Другое
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness



