How Cloud-Native Application Development Services Are Driving Digital Transformation in 2026
The rapid adoption of cloud technologies has changed how modern applications are built, deployed, and managed. The report from QKS Group, SPARK Matrix™: Cloud Native Application Development Services (CNADS), Q2 2025, highlights how enterprises are moving toward cloud-native architectures to improve agility, scalability, and innovation.
Click Here for More:
https://qksgroup.com/market-research/spark-matrix-cloud-native-application-development-services-cnads-q2-2025-8949
Understanding Cloud-Native Application Development
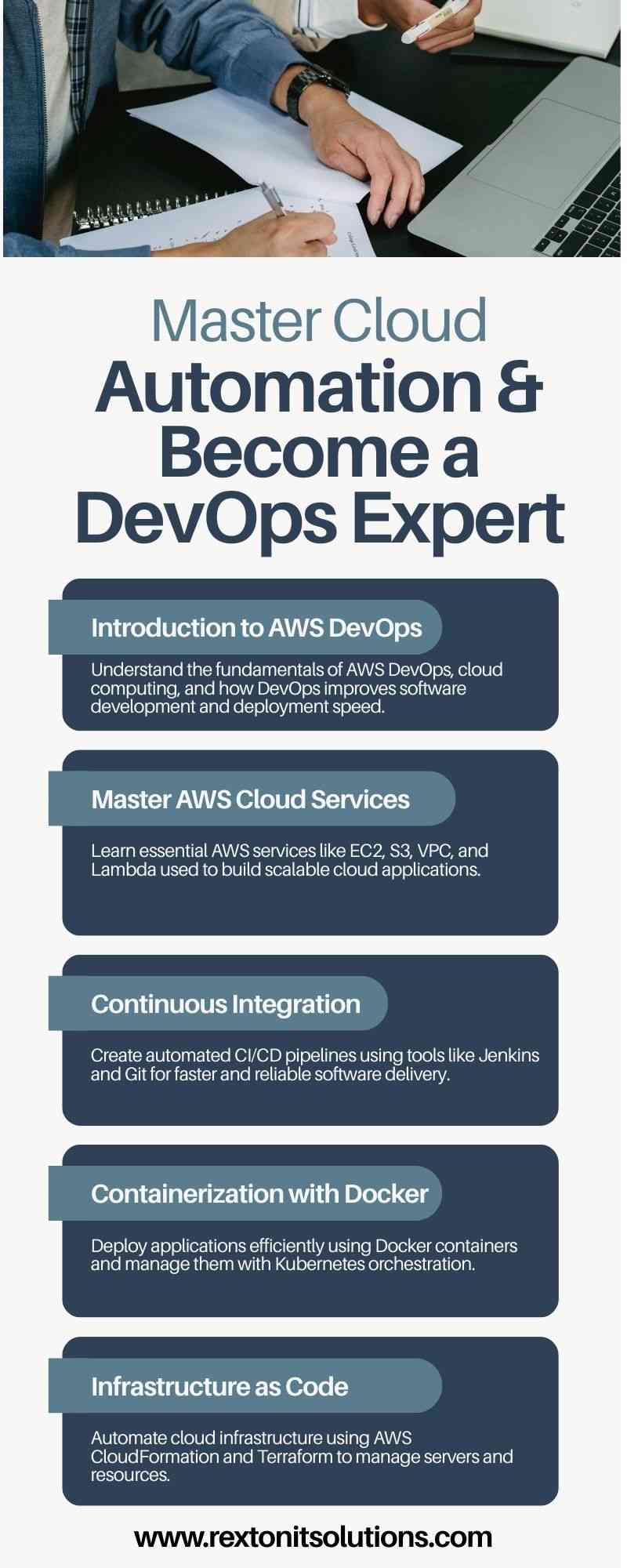
Cloud-native application development focuses on building applications using microservices, containers, Kubernetes, and DevOps practices. These applications are designed to run efficiently in dynamic cloud environments. Unlike traditional applications, cloud-native systems are highly scalable, resilient, and continuously updated.
The SPARK Matrix™ evaluates vendors based on two key parameters: technology excellence and customer impact. This framework helps enterprises compare service providers and select the right partner for their cloud transformation journey.
Key Market Trends in CNADS
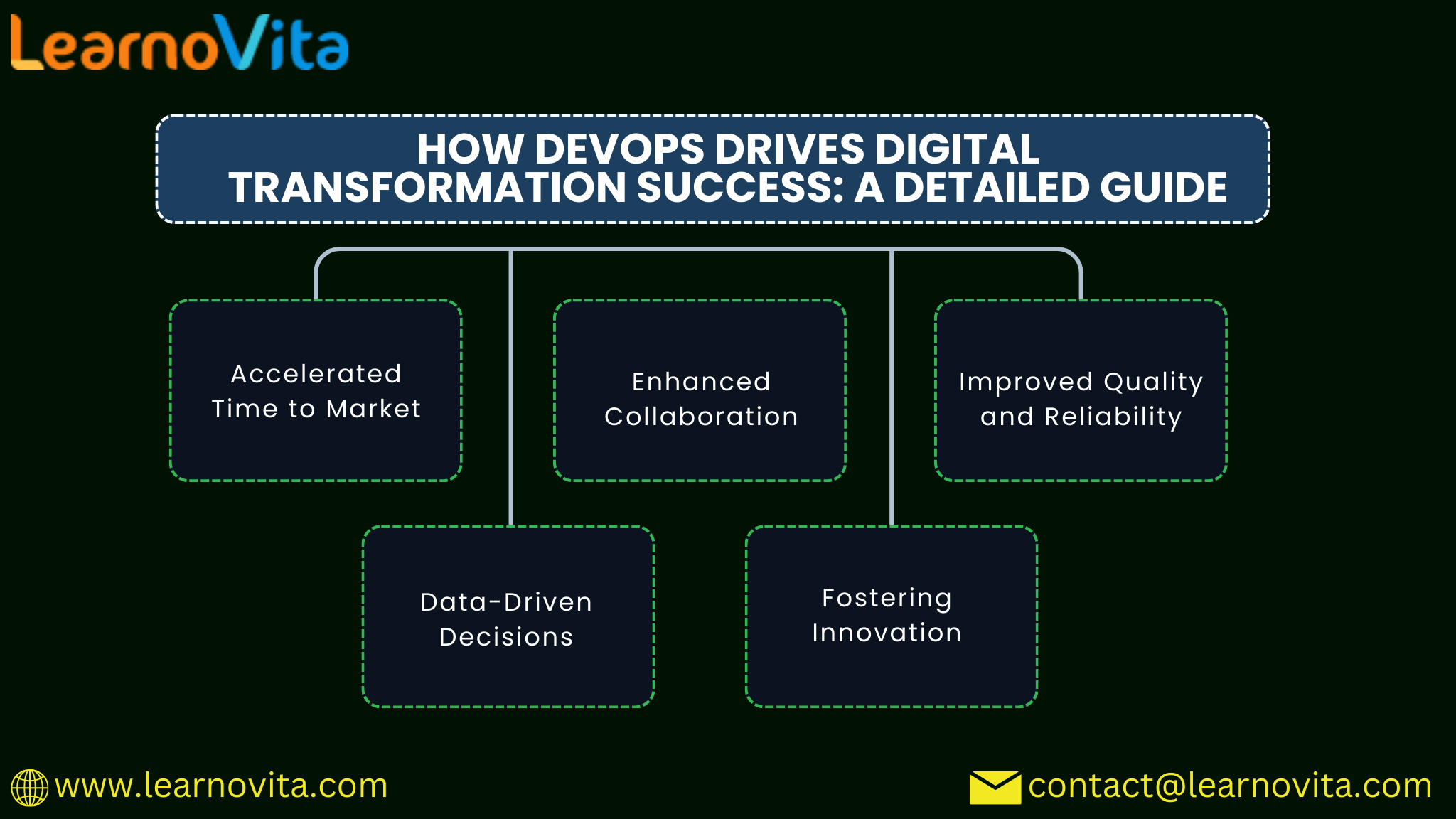
The CNADS market is evolving rapidly due to increasing demand for digital transformation. Enterprises are adopting cloud-native approaches to modernize legacy systems and improve time-to-market.
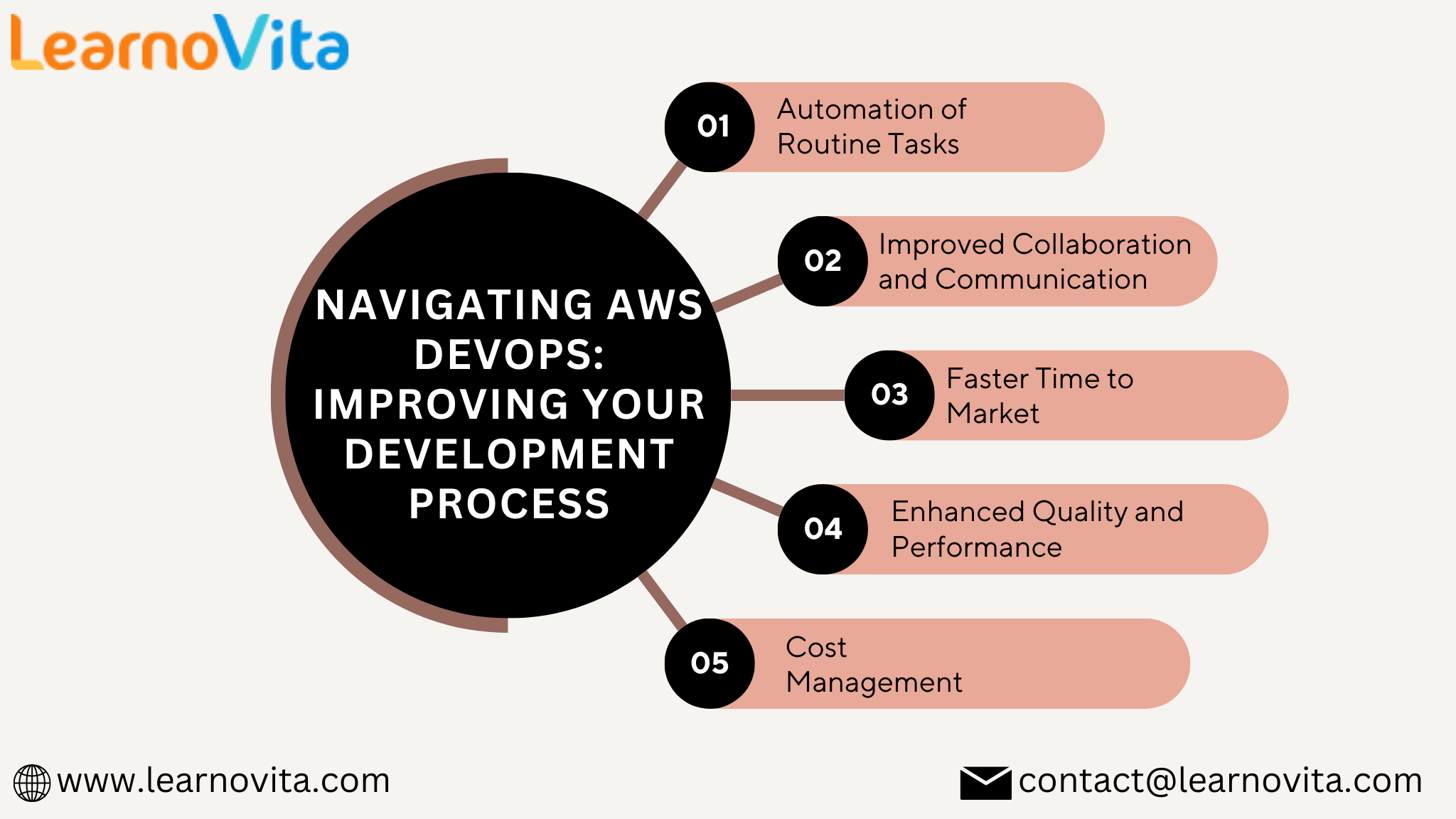
One of the major trends highlighted in the report is the growing use of AI-driven development tools. These tools help automate coding, testing, and deployment processes, making development faster and more efficient. AI also enables better decision-making through predictive analytics and intelligent monitoring.
Another important trend is the rise of containerization and Kubernetes orchestration. These technologies allow developers to package applications with all dependencies and deploy them consistently across environments. This improves portability and reduces operational complexity.
Additionally, organizations are focusing on DevSecOps practices, where security is integrated into every stage of the development lifecycle. This ensures that applications are secure by design and compliant with industry standards.
Market Share: Cloud-Native Application Protection Platform:
https://qksgroup.com/market-research/market-share-cloud-native-application-protection-platform-2025-worldwide-4212
Importance of Runtime Intelligence and Observability
Modern cloud-native environments are highly dynamic, making traditional monitoring methods less effective. The report emphasizes the importance of runtime intelligence, which provides real-time visibility into application behavior.
Advanced platforms now use technologies like telemetry, cloud logs, and AI analytics to monitor workloads, detect anomalies, and respond to threats quickly. This approach improves system reliability and reduces downtime.
For example, modern solutions analyze workload behavior, network traffic, and API interactions to identify security risks and performance issues in real time. This helps organizations maintain operational efficiency and ensure a seamless user experience.
Vendor Differentiation in the SPARK Matrix™
The SPARK Matrix™ highlights how leading vendors differentiate themselves through innovation and service capabilities. Key differentiators include:
End-to-end cloud-native services (consulting, development, migration, and management)
Strong Kubernetes and container expertise
Integration of AI and automation
Robust security and compliance frameworks
Industry-specific solutions
Vendors that combine these capabilities with strong customer support and global delivery models are positioned as leaders in the matrix.
Benefits for Enterprises
Adopting Cloud Native Application Development Services (CNADS) offers several benefits:
Faster innovation through continuous integration and delivery
Improved scalability to handle changing workloads
Better resilience with fault-tolerant architectures
Enhanced security with integrated DevSecOps practices
Cost optimization through efficient resource utilization
These advantages help businesses stay competitive in a digital-first world.
Market Forecast: Cloud-Native Application Protection Platform:
https://qksgroup.com/market-research/market-forecast-cloud-native-application-protection-platform-2026-2030-worldwide-4229
Conclusion
The SPARK Matrix™: Cloud Native Application Development Services, Q2 2025 report clearly shows that cloud-native development is no longer optional—it is essential for modern enterprises. Organizations that invest in cloud-native technologies and choose the right service partners can achieve higher efficiency, faster innovation, and stronger security.
As the market continues to evolve, the focus will shift toward AI-driven development, automation, and real-time observability. Enterprises must align their strategies with these trends to fully unlock the potential of cloud-native architectures.
#CloudNative #CloudNativeDevelopment #CNADS #ApplicationDevelopment #CloudComputing #DigitalTransformation #Kubernetes #Microservices #DevOps #DevSecOps #AIinTech #SoftwareDevelopment #AppModernization #CloudMigration #ScalableApps #CloudSecurity #PlatformEngineering #HybridCloud #MultiCloud #TechTrends
How Cloud-Native Application Development Services Are Driving Digital Transformation in 2026
The rapid adoption of cloud technologies has changed how modern applications are built, deployed, and managed. The report from QKS Group, SPARK Matrix™: Cloud Native Application Development Services (CNADS), Q2 2025, highlights how enterprises are moving toward cloud-native architectures to improve agility, scalability, and innovation.
Click Here for More: https://qksgroup.com/market-research/spark-matrix-cloud-native-application-development-services-cnads-q2-2025-8949
Understanding Cloud-Native Application Development
Cloud-native application development focuses on building applications using microservices, containers, Kubernetes, and DevOps practices. These applications are designed to run efficiently in dynamic cloud environments. Unlike traditional applications, cloud-native systems are highly scalable, resilient, and continuously updated.
The SPARK Matrix™ evaluates vendors based on two key parameters: technology excellence and customer impact. This framework helps enterprises compare service providers and select the right partner for their cloud transformation journey.
Key Market Trends in CNADS
The CNADS market is evolving rapidly due to increasing demand for digital transformation. Enterprises are adopting cloud-native approaches to modernize legacy systems and improve time-to-market.
One of the major trends highlighted in the report is the growing use of AI-driven development tools. These tools help automate coding, testing, and deployment processes, making development faster and more efficient. AI also enables better decision-making through predictive analytics and intelligent monitoring.
Another important trend is the rise of containerization and Kubernetes orchestration. These technologies allow developers to package applications with all dependencies and deploy them consistently across environments. This improves portability and reduces operational complexity.
Additionally, organizations are focusing on DevSecOps practices, where security is integrated into every stage of the development lifecycle. This ensures that applications are secure by design and compliant with industry standards.
Market Share: Cloud-Native Application Protection Platform: https://qksgroup.com/market-research/market-share-cloud-native-application-protection-platform-2025-worldwide-4212
Importance of Runtime Intelligence and Observability
Modern cloud-native environments are highly dynamic, making traditional monitoring methods less effective. The report emphasizes the importance of runtime intelligence, which provides real-time visibility into application behavior.
Advanced platforms now use technologies like telemetry, cloud logs, and AI analytics to monitor workloads, detect anomalies, and respond to threats quickly. This approach improves system reliability and reduces downtime.
For example, modern solutions analyze workload behavior, network traffic, and API interactions to identify security risks and performance issues in real time. This helps organizations maintain operational efficiency and ensure a seamless user experience.
Vendor Differentiation in the SPARK Matrix™
The SPARK Matrix™ highlights how leading vendors differentiate themselves through innovation and service capabilities. Key differentiators include:
End-to-end cloud-native services (consulting, development, migration, and management)
Strong Kubernetes and container expertise
Integration of AI and automation
Robust security and compliance frameworks
Industry-specific solutions
Vendors that combine these capabilities with strong customer support and global delivery models are positioned as leaders in the matrix.
Benefits for Enterprises
Adopting Cloud Native Application Development Services (CNADS) offers several benefits:
Faster innovation through continuous integration and delivery
Improved scalability to handle changing workloads
Better resilience with fault-tolerant architectures
Enhanced security with integrated DevSecOps practices
Cost optimization through efficient resource utilization
These advantages help businesses stay competitive in a digital-first world.
Market Forecast: Cloud-Native Application Protection Platform: https://qksgroup.com/market-research/market-forecast-cloud-native-application-protection-platform-2026-2030-worldwide-4229
Conclusion
The SPARK Matrix™: Cloud Native Application Development Services, Q2 2025 report clearly shows that cloud-native development is no longer optional—it is essential for modern enterprises. Organizations that invest in cloud-native technologies and choose the right service partners can achieve higher efficiency, faster innovation, and stronger security.
As the market continues to evolve, the focus will shift toward AI-driven development, automation, and real-time observability. Enterprises must align their strategies with these trends to fully unlock the potential of cloud-native architectures.
#CloudNative #CloudNativeDevelopment #CNADS #ApplicationDevelopment #CloudComputing #DigitalTransformation #Kubernetes #Microservices #DevOps #DevSecOps #AIinTech #SoftwareDevelopment #AppModernization #CloudMigration #ScalableApps #CloudSecurity #PlatformEngineering #HybridCloud #MultiCloud #TechTrends